Create a policy assignment to identify non-compliant resources
Create a policy assignment
In this lab, you create a policy assignment and assign the Audit VMs that do not use managed disks policy definition.
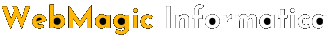
- Launch the Azure Policy service in the Azure portal by selecting All services, then searching for and selecting Policy.
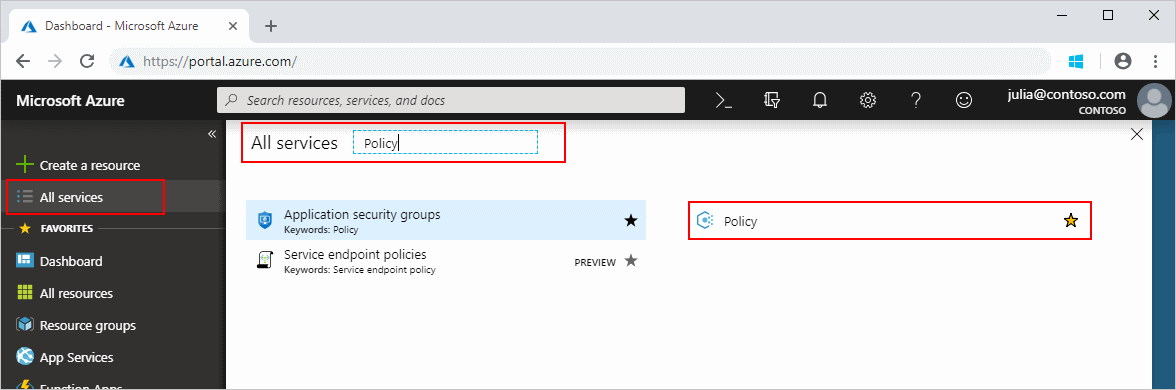
- Select Assignments on the left side of the Azure Policy page. An assignment is a policy that has been assigned to take place within a specific scope.
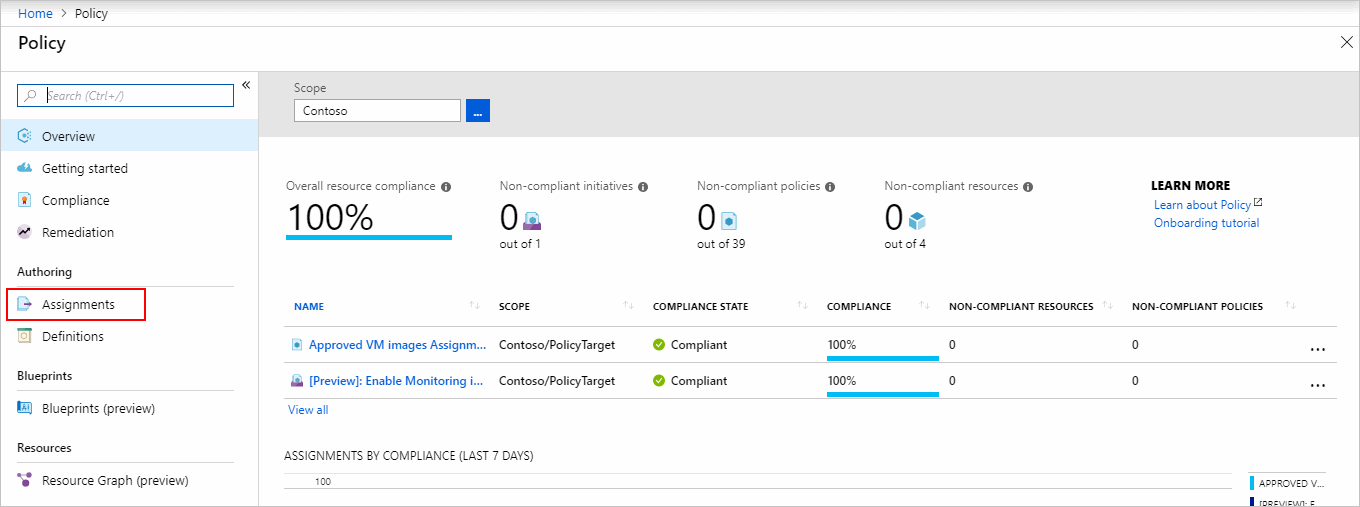
- Select Assign Policy from the top of the Policy – Assignments page.
- On the Assign Policy page, set the Scope by selecting the ellipsis and then selecting either a management group or subscription. Optionally, select a resource group. A scope determines what resources or grouping of resources the policy assignment gets enforced on. Then use the Select button at the bottom of the Scope page.This example uses the Contoso subscription. Your subscription will differ.
- Resources can be excluded based on the Scope. Exclusions start at one level lower than the level of the Scope. Exclusions are optional, so leave it blank for now.
- Select the Policy definition ellipsis to open the list of available definitions. Azure Policy comes with built-in policy definitions you can use. Many are available, such as:
- Enforce tag and its value
- Apply tag and its value
- Inherit a tag from the resource group if missing
- Search through the policy definitions list to find the Audit VMs that do not use managed disks definition. Select that policy and then use the Select button.

- The Assignment name is automatically populated with the policy name you selected, but you can change it. For this example, leave Audit VMs that do not use managed disks. You can also add an optional Description. The description provides details about this policy assignment. Assigned by will automatically fill based on who is logged in. This field is optional, so custom values can be entered.
- Leave policy enforcement Enabled.
- Select Next at the bottom of the page or the Parameters tab at the top of the page to move to the next segment of the assignment wizard.
- If the policy definition selected on the Basics tab included parameters, they are configured on this tab. Since the Audit VMs that do not use managed disks has no parameters, select Next at the bottom of the page or the Remediation tab at the top of the page to move to the next segment of the assignment wizard.
- Leave Create a Managed Identity unchecked. This box must be checked when the policy or initiative includes a policy with either the
deployIfNotExistsormodifyeffect. As the policy used for this quickstart doesn’t, leave it blank. - Select Next at the bottom of the page or the Non-compliance messages tab at the top of the page to move to the next segment of the assignment wizard.
- Set the Non-compliance message to Virtual machines should use a managed disk. This custom message is displayed when a resource is denied or for non-compliant resources during regular evaluation.
- Select Next at the bottom of the page or the Review + Create tab at the top of the page to move to the next segment of the assignment wizard.
- Review the selected options, then select Create at the bottom of the page.
Identify non-compliant resources
- Select Compliance in the left side of the page. Then locate the Audit VMs that do not use managed disks policy assignment you created.

- If there are any existing resources that aren’t compliant with this new assignment, they appear under Non-compliant resources.
Tag:Azure