VPC Networking Fundamentals Lab
Explore the default network
View the subnets
The default network has a subnet in each Google Cloud region.
In the Console, navigate to Navigation menu (![]() ) > VPC network > VPC networks.
) > VPC network > VPC networks.
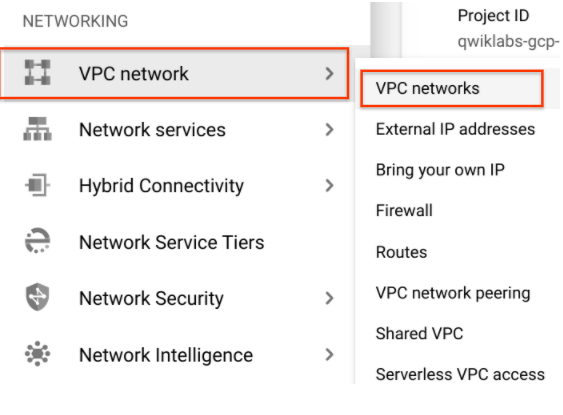
Notice the default network with its subnets.
View the routes
Routes tell VM instances and the VPC network how to send traffic from an instance to a destination, either inside the network or outside of Google Cloud. Each VPC network comes with some default routes to route traffic among its subnets and send traffic from eligible instances to the Internet.
In the left pane, click on Routes.
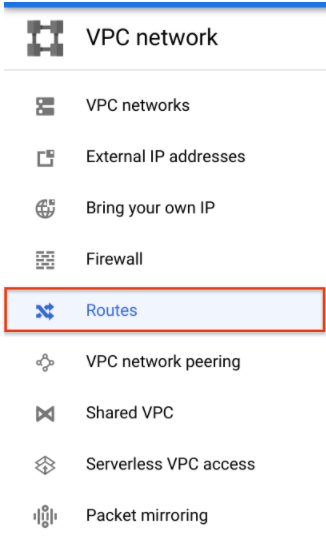
Notice that there is a route for each subnet and one for the Default internet gateway (0.0.0.0./0).
View the firewall rules
Each VPC network implements a distributed virtual firewall that you can configure. Firewall rules allow you to control which packets are allowed to travel to which destinations. Every VPC network has two implied firewall rules that block all incoming connections and allow all outgoing connections.
In the left pane, click on Firewall.
Notice that there are 4 Ingress firewall rules for the default network:
- default-allow-icmp
- default-allow-internal
- default-allow-rdp
- default-allow-ssh
Delete the default network
- In the left pane, click on Firewall.
- Select all firewall rules and click DELETE. Then click DELETE to confirm the deletion.
- In the left pane, click on VPC networks.
- Click on the default network.
- Click Delete VPC network at the top of the page, then click DELETE to confirm the deletion of the default network.Wait for the network to be deleted before moving on.
- In the left pane, click on Routes.Notice that there are no routes. You may need to click the Refresh button at the top of the page.
Try to create a VM instance
- In the Console, navigate to Navigation menu > Compute Engine > VM instances, and then click +CREATE INSTANCE to create a VM instance.
- Leave all the values at their default and click Create.
Notice the error. - Under the Firewall section, click NETWORKING, DISKS, SECURITY, MANAGEMENT, SOLE-TENANCY, and then click Networking.
- Notice the error under Network interfaces.
- Click Cancel.
Create a VPC network and VM instances
Create an auto mode VPC network with Firewall rules
- In the Console, navigate to Navigation menu > VPC network > VPC networks, and then click +CREATE VPC NETWORK.
- Set the Name to
mynetwork. - For Subnet creation mode, click Automatic.
Auto mode networks create subnets in each region automatically. - For Firewall rules, check all available rules.
These are the same standard firewall rules that the default network had. - Click CREATE, then wait for mynetwork to be created.
Notice that a subnet was created for each region. - Click on the mynetwork name and record the IP address range for the subnets in us-central1 and europe-west1. You will refer to these in the next steps.
Create a VM instance in us-central1
- In the Console, navigate to Navigation menu > Compute Engine > VM instances, and then click +CREATE INSTANCE.
- Set the following values, leaving all others at their defaults:
Name: mynet-us-vm
Region: us-central1
Zone: us-central1-c
Series: N1
Machine type: n1-standard-1 (1 vCPU) - Click Create, then wait for the instance to be created.
- Verify that the Internal IP was assigned from the IP address range for the subnet in us-central1 (10.128.0.0/20).
Create a VM instance in europe-west1
- Click +CREATE INSTANCE.
- Set the following values, leaving all others at their defaults:
Name: mynet-eu-vm
Region: europe-west1
Zone: europe-west1-b
Series: N1
Machine type: n1-standard-1 (1 vCPU) - Click Create, then wait for the instance to be created.
- Verify that the Internal IP was assigned from the IP address range for the subnet in europe-west1 (10.132.0.0/20).
Explore the connectivity for VM instances
Verify connectivity for the VM instances
- In the Console, navigate to Navigation menu (
) > Compute Engine > VM instances.Note the external and internal IP addresses for mynet-eu-vm.
- For mynet-us-vm, click SSH to launch a terminal and connect. You may have to click SSH twice.You are able to SSH because of the allow-ssh firewall rule, which allows incoming traffic from anywhere (0.0.0.0/0) for tcp:22.
- To test connectivity to mynet-eu-vm‘s internal IP, run the following command using mynet-eu-vm‘s internal IP:
ping -c 3 <Enter mynet-eu-vm's internal IP here>
- To test connectivity to mynet-eu-vm‘s external IP, run the following command using mynet-eu-vm‘s external IP:
ping -c 3 <Enter mynet-eu-vm's external IP here>
Remove the allow-icmp firewall rules
- In the Console, navigate to Navigation menu (
) > VPC network > Firewall.
- Check the mynetwork-allow-icmp rule.
- Click DELETE, then click DELETE to confirm the deletion.Wait for the firewall rule to be deleted.
- Return to the mynet-us-vm SSH terminal.
- To test connectivity to mynet-eu-vm‘s internal IP, run the following command using mynet-eu-vm‘s internal IP:
ping -c 3 <Enter mynet-eu-vm's internal IP here>
- To test connectivity to mynet-eu-vm’s external IP, run the following command using mynet-eu-vm’s external IP:
ping -c 3 <Enter mynet-eu-vm's external IP here
Remove the allow-custom firewall rules
- In the Console, navigate to Navigation menu (
) > VPC network > Firewall.
- Check the mynetwork-allow-custom rule and then click DELETE. Click DELETE to confirm the deletion.Wait for the firewall rule to be deleted.
- Return to the mynet-us-vm SSH terminal.
- To test connectivity to mynet-eu-vm‘s internal IP, run the following command using mynet-eu-vm‘s internal IP:
ping -c 3 <Enter mynet-eu-vm's internal IP here>
- Close the SSH terminal:
exit
Remove the allow-ssh firewall rules
- In the Console, navigate to Navigation menu > VPC network > Firewall.
- Check the mynetwork-allow-ssh rule and then click DELETE. Click DELETE to confirm the deletion.Wait for the firewall rule to be deleted.
- In the Console, navigate to Navigation menu > Compute Engine > VM instances.
- For mynet-us-vm, click SSH to launch a terminal and connect.
Tag:Google Cloud